네이버 클라우드 플랫폼
모의침투 테스트(Penetration Testing) 정책(약관)
◼︎ 제 1 조 (개요 및 목적)
본 정책은 네이버클라우드 주식회사(이하 ‘회사’)가 제공하는 네이버 클라우드 플랫폼 서비스에 대한 모의 침투 테스트를 수행함에 있어 회사와 이용고객(이하 ‘고객’)간의 권리와 의무 및 기타 필요한 사항을 규정하는데 그 목적이 있습니다. 모든 모의 침투 테스트는 아래에서 설명하는 네이버 클라우드 플랫폼 모의 침투 테스트 정책을 따라야 합니다.
◼︎ 제 2 조 (기본 조건)
1.네이버 클라우드 플랫폼 구성 요소에 대한 모의 침투 테스트는 반드시 회사와 사전 협의가 필요합니다. 협의되지 않은 모의 침투 테스트의 경우, 회사는 사전 통보없이 테스트를 차단할 수 있고 해당 고객 계정을 일시 중단할 수 있습니다.
2.모든 모의 침투 테스트의 대상 범위는 해당 고객의 리소스(자산)로 제한되며 다른 고객에게 의도하지 않은 결과가 발생하지 않도록 주의해야 합니다.
3.고객은 모의 침투 테스트 수행을 위해 사용한 도구와 서비스가 본 정책에서 제시하고 있는 범위 내에 올바르게 구성되고 의도한대로 작동하는지 사전에 확인 및 입증하여야 합니다.
4.모의 침투 테스트 과정에서 네이버 클라우드 플랫폼 서비스와 관련된 잠재적인 보안 문제(취약점)를 발견하면 즉시 회사의 보안팀(dl_ncp_ms@navercorp.com)에 문의해야 합니다. 또한 문의 내용에 대해 회사로부터 회사 명의의 공식 회신을 받을 때까지 보안 문제(취약점)를 제3자 또는 일반 대중에 공개하여서는 안 됩니다.
5.고객이 본 정책을 위반할 경우 고객의 모든 계정이 일시 중단되거나 종료되고 법적 조치를 받을 수 있습니다.
6.고객이 본 정책을 위반하여 회사 및 다른 고객의 데이터에 대한 손상이나 손해를 발생시킨 경우 이에 대한 책임은 고객에게 있습니다.
7.회사는 고객 및 고객의 리소스(자산)를 보호하고 서비스 품질을 보장합니다.
◼︎ 제 3 조 (제한 사항)
1. 다른 고객에게 속한 리소스 검사 또는 테스트
2. 다른 고객의 데이터에 대한 접근
3. 다량의 트래픽을 생성하는 자동화 도구 또는 서비스를 이용한 테스트 수행
4. 네이버 클라우드 플랫폼 이용 약관을 위반하는 방식의 서비스 사용
5. 회사 및 회사 임직원에 대한 피싱 또는 기타 Social Engineering 공격 시도
6. 모든 종류의 서비스 거부(DoS, Denial of Service) 테스트 수행
① 예외 사항
(ㄱ) Security Monitoring 상품 이용 고객에 한하여 한국인터넷진흥원(KISA), 금융보안원(FSI) 등 국가 지정 침해사고 대응 기관을 통한 모의 훈련은 회사와 사전 협의 하에 가능합니다.
② 서비스 거부(DoS) 테스트는 아래의 범위로 제한됩니다.
(ㄱ) 대역폭 : 사전 계약된 약정 용량 범위 내
(ㄴ) 빈도 : 최대 연 2회
(ㄷ) L4 layer의 DoS 테스트만 지원
◼︎ 제 4 조 (서비스 범위)
1. 회사는 고객 요청 시, 모의 침투 테스트에서 사용되는 고객의 Source IP에 대한 예외 처리를 적용할 수 있습니다.
(ㄱ) 단, IP 예외 처리 시, 해당 IP에 대한 탐지 및 차단 로그는 고객 확인이 불가합니다.
(ㄴ) Security Monitoring 상품 내 이용 중인 보안 서비스의 탐지 및 차단 로그에 대한 확인이 필요한 고객의 경우, IP 예외 처리 요청을 지양해 주시기 바랍니다.
2. 회사는 모의 침투 테스트 관련 보안 로그를 제공하지 않습니다. 보안 로그가 필요한 고객은 네이버 클라우드 플랫폼 Console 내 Security Monitoring 또는 Cloud Log Analytics 상품을 통해 직접 보안 로그를 확인하여야 합니다.
(ㄱ) 단, Classic 플랫폼 환경에서 Security Monitoring 상품을 이용 중인 경우, 회사는 고객 요청 시 고객이 이용 중인 보안 서비스에 대한 탐지 및 차단 로그를 제공합니다.
(ㄴ) Cloud Log Analytics 상품을 통해 보안 로그를 확인하고자 하는 고객은 사전에 Cloud Log Analytics 상품 신청 및 Security Monitoring 보안 로그 저장(연동) 기능을 활성화하여야 합니다.
3. 회사는 모의 침투 테스트 기간 내 고객을 위한 전담 보안 전문가를 배정하지 않습니다.
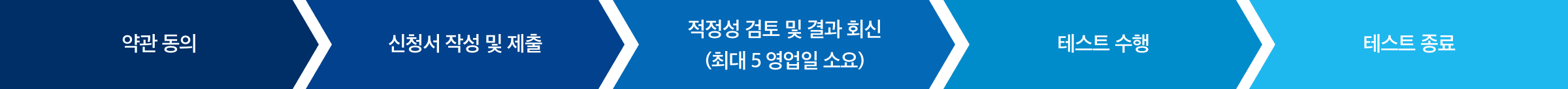
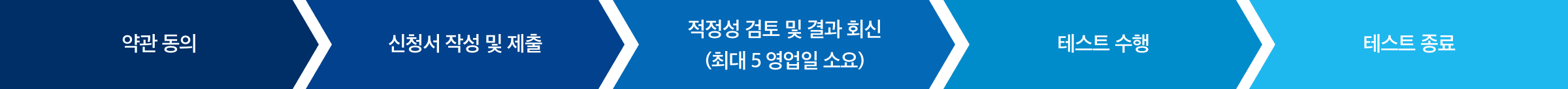
◼︎ 제 5 조 (사전 협의 요청 방법)
1. 모의 침투 테스트 관련 계정(메인), 일정, 테스트 유형, 연락처 및 계획된 이벤트에 대한 상세 설명(대상 자산, IP 등)을 포함한 ‘모의 침투 테스트 신청서’를 작성하여 사전 협의를 신청해 주시기 바랍니다.
2. 회사는 적정성 평가를 위하여 추가 정보를 고객에게 요청할 수 있습니다.
3. 회사는 고객의 요청 내용을 바탕으로 테스트 적정성 여부를 검토 후 5영업일 이내에 결과를 회신 드립니다. 다만, 회사는 추가 정보 요청 또는 요청 사항에 대한 확인 등을 위해 필요한 경우 회신 기한을 7일 이내 범위에서 연장할 수 있으며 연장 시에는 메일로 통보합니다.